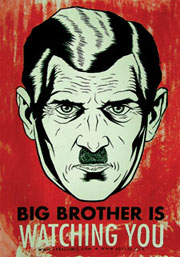
George Orwell’s ‘The Big Brother’ need not necessarily be a huge poster with an “enormous face gazing from the wall”. In this world of 0s and 1s, that eye can follow us even through a malicious link.
There was a time in world history when the British armies trampled over several countries to turn them into colonies. The late 16th to 18th century world was conquered by ‘companies’ with armies. Then came the 20th and 21st centuries where the superpowers switched to a more convenient ways of spreading their claws. They started hijacking the economies of the underdeveloped countries.
However, in the digital age, potential empires are just a click away. Any government (even India’s own government) with shrewd surveillance can turn countries into colonies and people into slaves. And this is how the first world countries in the neo-liberal ‘globalised’ world gang up against dissenters all across the globe.
This article deals with one such deadly nexus: the USA-Israel nexus. The NSO Group is a spawn of the same.
Dissecting the NSO Group: TheNSO Group, based in Herzliya, near Tel Aviv, in Israel, calls itself a tech company which “develops best-in-class technology” that “helps authorised government agencies prevent and investigate terrorism and crime to save thousands of lives around the globe”. The NSO’s leadership works at three levels: Board of Directors, Senior Advisors and Management.
The Board of Directors consist of serial entrepreneurs and owners of investment firms who have served in the US, Europe, China, India and Russia. The level of Senior Advisors is what unveils the stark naked truth behind this ‘tech-company’. It consists of Gov. Tom Ridge (43rd Governor of Pennsylvania) who was the first US Secretary of Homeland Security, Gerard Araud, who is a retired career diplomat and has held numerous positions within the French ministry of foreign affairs, Juliette Kayyem, who presently serves in the faculty of Harvard University’s Kennedy School of Government, Daniel Reisner, who has served as the head of IDF’s International Law Department for almost a decade, and Buky Carmeli, who is the former director-general and founder of the Israeli National Cyber Security Authority (NCSA), under the prime minister of the state of Israel, and the former head of MOD Cyber Defense Division.
Also, the history of NSO is not painted on a crystal-clear canvas. Even its origin is dubious. Its founders are believed to be ex-members of Unit 8200, the Israeli Intelligence Corps unit which was essentially responsible for collecting signals intelligence. The company has had ties with the governments of many countries.
The situation of snooping is a million times grave. Pegasus was allegedly involved in spying on journalist Jamal Khashoggi, who was killed in the Saudi Arabian consulate in Istanbul on October 2, 2018.
The government of Mexico declared a contract of $20 million with NSO in 2012. Its surveillance technology was sold to the government of Panama in 2015. The NSO was sold to an American firm, Franciso Partners, for $130 million.
In 2019, Francisco Partners sold a 60 per cent majority stake of NSO back to co-founders Shalev Hulio and Omri Lavie. In 2019, NSO allegedly struck a nexus with the government of Saudi Arabia which was behind the surveillance and murder of journalist Jamal Khashoggi.
Pegasus — The digital burglar: Pegasus is a spyware developed by the NSO group that can be installed on devices running all versions of iOS (Apple’s mobile operating system). The world came to know about Pegasus when attempts were made to install it on an iPhone of an Arab human rights activist, Ahmed Mansoor.
Mansoor received a text message which gave a hot tip about torture and human rights violations rampant in the prisons of the United Arab Emirates. He received a link along with the message. Mansoor sent the link to the Citizen Lab and the investigation in August 2016 brought out the existence of the spyware in the public domain. It was revealed that upon clicking on a malicious link, Pegasus secretly enables a jailbreak on the device and can perpetuate the following:
- Reading text messages
- Tracking calls
- Collecting passwords
- Tracing the location of the phone
- Accessing the target device’s microphone(s)
- Video camera(s)
- Gathering information from apps including iMessage, Gmail, Viber, Facebook, WhatsApp, Telegram and Skype
- Switching on cameras and microphones
The Pegasus attack is called the ‘most sophisticated’ smartphone attack ever.
It’s never the first time: TheAhmed Masoor case is just the tip of the iceberg. The situation of snooping is actually a million times grave. Pegasus was allegedly involved in spying on the journalist and a critic of the Saudi government, Jamal Khashoggi, who was brutally killed in the Saudi Arabian consulate in Istanbul on October 2, 2018.
Omar Abdulaziz, his fellow dissenter, filed a suit against the NSO in Tel Aviv. He accused the Saudi authorities of monitoring the communications between him and Khashoggi with the help of NSO’s software.
PART TWO: Pegasus — The Shadow of Snooping
The claws of the NSO group reached India in April-May 2019 when the malware was sent to approximately 1400 mobile phones using the WhatsApp servers in the United States and other parts of the world. WhatsApp filed a lawsuit in the Northern District of California court on October 29, 2019, alleging that WhatsApp accounts were created to initiate voice calls using the remote WhatsApp servers to inject the malware onto the mobile phones.
The malware created a connection between the mobile phone and the remote server. The lawsuit also claimed that the malware was unable to break the “end to end encryption of WhatsApp” and it could access the messages only after it was decrypted on target devices.
Even its origin is dubious. NSO founders are believed to be ex-members of Unit 8200, the Israeli Intelligence Corps unit which was responsible for collecting signals intelligence. The company has had ties with the governments of many countries.
The WhatsApp accounts were allegedly created ‘using telephone numbers registered in different countries, including Cyprus, Israel, Brazil, Indonesia, Sweden and the Netherlands’. These WhatsApp accounts also leased internet services in different countries, including in the US, for distributing the malware across the world.
The basis of the allegation on the NSO group is the fact that the IP address of one of the malicious servers was previously associated with subdomains of the group.
The lawsuit alleges that the NSO group, “reverse-engineered the app” and emulated legitimate WhatsApp network traffic to transmit the malware without being detected by the technical restrictions on the WhatsApp Signalling Servers. The call initiation messages were formatted to imitate a legitimate call. The malicious code was secretly hidden inside the call and it broke into the memory of the device even if the call was not answered.
The Government of India — A possible ally: The documents filed along with the lawsuit contain a signed contract with Ghana’s National Communications Authority which states that the Pegasus software can only be deployed with a written sanction from Israel’s Ministry of Defense. The NSO user guide states that installing Pegasus is a “laborious, expensive and time-consuming process”. It requires at least 15 weeks to install, test and then deploy. It also includes a two-week training course and a one-week on-site handover. Four weeks in the first phase are used for ‘Local Network Adjustments’ to integrate the malware with local infrastructures and systems.
In order to break into the phones of any country, NSO technicians require considerable time to penetrate into the system. This puts the government of India under a cloud of suspicion given the fact that the NSO group usually sells its products to governments only.
Some important points need to be underlined here.
One, in order to break into the phones of any country, the NSO technicians require a considerable amount of time to penetrate into the system. This puts the government of India under a cloud of suspicion given the fact that the NSO group usually sells its products to the governments only.
Two, there is evidence that in December 2015, Infralocks Development Ltd, a Ghanaian subsidiary of Israel’s NSO Group, signed an agreement to sell the Pegasus software to Ghana’s National Communications Authority for a fee of $8 million along with a service contract worth $1.76 million a year to be paid through an “untraceable payment method’ comprising of a credit card with a $4000 balance linked to a passport, a prepaid untraceable SIM card, and a utility bill with an address linked to the passport.

Indeed, such a heavy payment along with the infrastructure to legitimise the snooping, cannot really be served with the government being totally oblivious to it.
Three, the targets included Dalit and Adivasi rights activists, lawyers and intellectuals involved in the Bhima-Koregaon case, which has always been a card used to muzzle dissent by booking activists under draconian laws like UAPA and Sedition.
Four, despite the serious allegation of Indian activists and intellectuals being snooped on under the sanction of the government of Israel, Ravishankar Prasad, the Union Minister for Law & Justice, Communications, Electronics & Information Technology, tweeted that the Indian government has a “well-established protocol” for snooping on citizens. He neither confirmed nor denied the use of Pegasus.
Five, if the government is able to access an individual’s phones and computers then it is also capable of planting evidence in it. Shalini Gera, a lawyer who is also the Chhattisgarh Secretary of the People’s Union for Civil Liberties (PUCL), raised this serious question in a conversation with Huffington Post.
Six, the Indian government was informed about the vulnerabilities in the WhatsApp’s service in May 2019. It chose to not reply, let alone investigate. After four months, WhatsApp again informed the government agencies in writing that 121 Indian individuals have been targeted.
The Deadly Nexus: This plot is a cob-web(site) whose threads are produced by fascist and dictatorial governments and are entangled using the loopholes of technology. A ‘Digital India’ which claims to have achieved around 40 per cent internet penetration (Source: Market Research Agency, Kantar, IMRB), is still trapped in the jaws of cybercrime and surveillance.
The situation is grave but the Indian government seems to be unalarmed. It perhaps has chosen to be. The demand for a tightened digital security needs to be pressed by the citizens until the government chooses to not barge into the privacy of people behind the veil of ‘national security’. The government needs to be reminded that the Right to Privacy is now a fundamental right and its high time that under the umbrella of ‘national security’ the government should also include the security of the people of the nation.
GhanaIndiaInternetIsraelMobileNSOPegasusServeillanceSnoopingWhatsapp